Imagine you’re trying to send a quick text message, but the phone network is so clogged that it takes five minutes and costs $5. That was daily life on Ethereum during its peak congestion periods. Enter sidechains: independent blockchains that run parallel to the main network, offering lightning-fast speeds and pennies in fees. But here’s the catch-how do your assets actually move between these two worlds without getting lost or stolen?
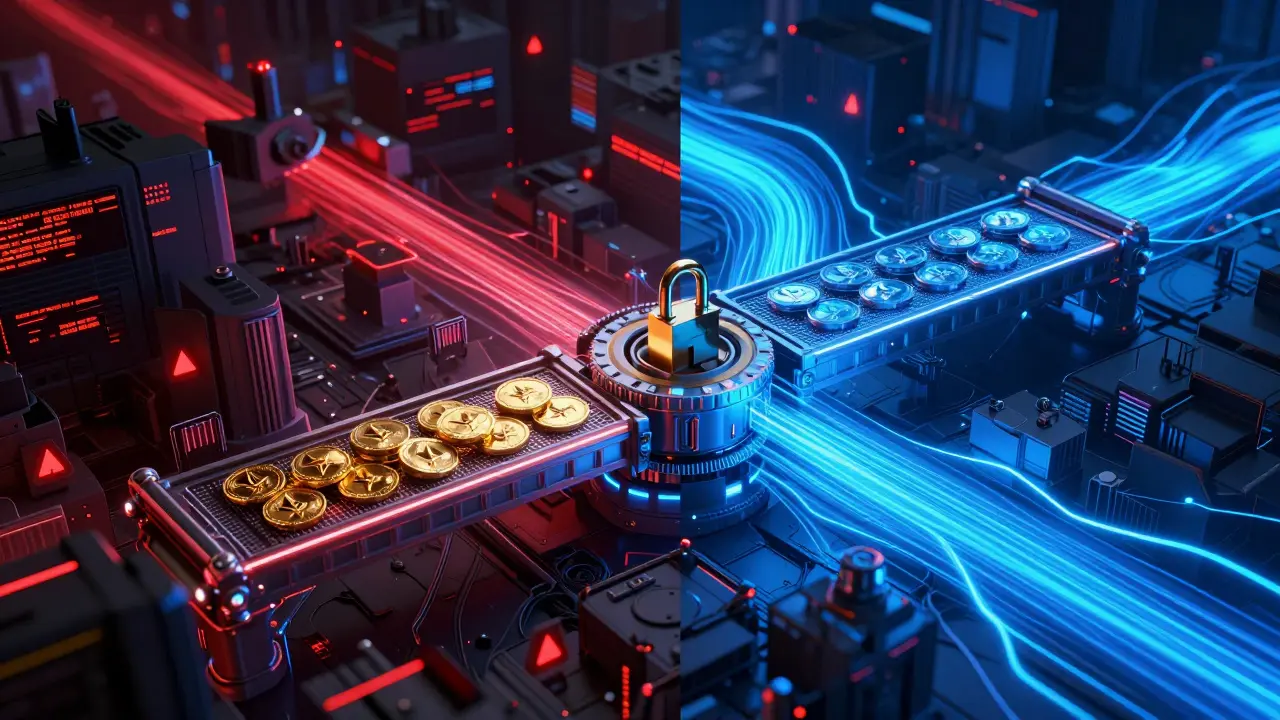
The answer isn’t magic; it’s cryptography. Specifically, a mechanism called the two-way peg. This is the bridge that locks your coins on the main chain and mints equivalent tokens on the sidechain. It sounds simple, but under the hood, it involves complex smart contracts, validator nodes, and significant security risks. Let’s break down exactly how this connection works, why it matters for your wallet, and what happens when things go wrong.
The Core Mechanism: How the Two-Way Peg Works
To understand the connection, you first need to visualize the flow of assets. A sidechain doesn’t just copy data from the main blockchain; it creates a separate ledger with its own rules. The two-way peg is the gatekeeper that allows value to enter and exit this isolated environment securely.
Here is the step-by-step process of moving assets from a mainchain (like Ethereum) to a sidechain (like Polygon):
- Locking: You initiate a transfer by sending your cryptocurrency (e.g., ETH) to a specific smart contract address on the mainchain. This contract acts as a vault. Your funds are not destroyed; they are frozen there.
- Verification: The sidechain’s network monitors the mainchain. Once it detects the deposit and sees enough confirmations (usually 100-200 blocks for security), it validates the transaction.
- Minting: The sidechain mints an equivalent amount of wrapped tokens (e.g., Wrapped ETH) into your sidechain wallet. These tokens represent your locked assets on the other chain.
- Usage: You can now trade, play games, or use dApps on the sidechain with near-zero fees.
- Burning & Unlocking: To return to the mainchain, you burn the wrapped tokens on the sidechain. The sidechain sends a proof to the mainchain smart contract, which then unlocks your original ETH and releases it back to your mainnet wallet.
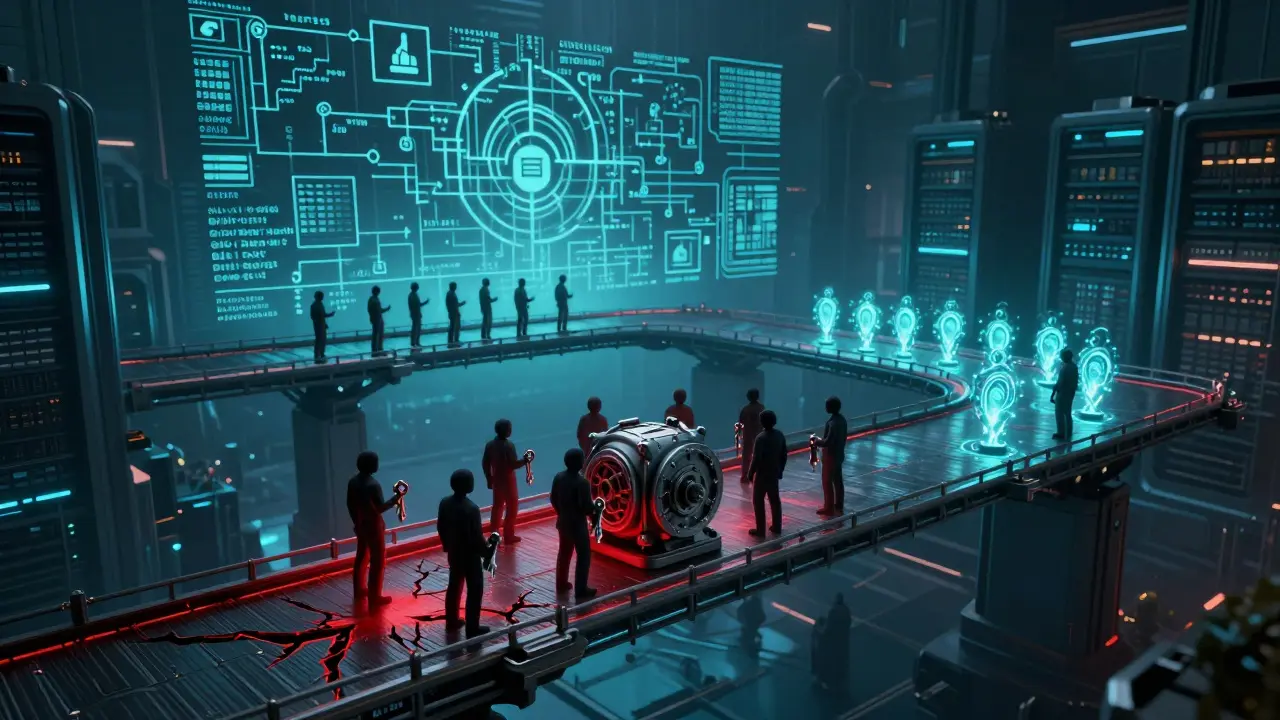
This process relies heavily on trust. Who watches the vault? Who ensures the minting is accurate? In most current implementations, this role falls to a group of validator nodes.
The Role of Validators and Bridge Types
Not all bridges are created equal. The security of your assets depends entirely on the type of bridge connecting the sidechain to the mainchain. There are three primary models, each with different risk profiles.
| Bridge Type | Security Model | Speed | Risk Level | Example |
|---|---|---|---|---|
| Federated | Relies on a multi-signature wallet controlled by a set number of validators (e.g., 2/3 consensus). | Fast (seconds to minutes) | High (if majority collude) | Ronin Network |
| Proof-of-Stake (PoS) | Validators stake native tokens. Malicious behavior leads to "slashing" (loss of stake). | Medium (minutes) | Medium | Polygon PoS |
| Trustless (Zero-Knowledge) | Uses cryptographic proofs (ZK-proofs) to verify transactions without trusting validators. | Slower (complex computation) | Lowest (mathematical security) | StarkNet, zkSync |
In a federated bridge, you are trusting a small group of entities. If 67% of them agree to steal the funds, they can. This happened famously with the Ronin bridge hack in 2022, where attackers compromised several validator keys. In contrast, a trustless bridge uses math, not people, to secure the transfer. While slower, it eliminates the human element of corruption.
Most popular sidechains like Polygon use a hybrid approach. They employ checkpoint mechanisms where validators submit cryptographic proofs to the Ethereum mainnet every few minutes. This allows the mainchain to theoretically freeze the bridge if fraud is detected, though this process is often slow and cumbersome.
Why Use Sidechains? The Scalability Trilemma
You might ask: why not just upgrade the main blockchain? The answer lies in the blockchain trilemma. A blockchain can only optimize for two of three things at once: Security, Decentralization, and Scalability.
Ethereum prioritizes Security and Decentralization, which limits its throughput to about 30 transactions per second (TPS). Sidechains sacrifice some degree of mainchain security to gain massive scalability. For example, Polygon can handle over 7,000 TPS. This makes sidechains ideal for high-frequency activities like gaming, NFT trading, and micro-transactions, where paying $10 in gas fees for a $2 item is absurd.
However, this trade-off is real. As Vitalik Buterin has noted, sidechains are a "different risk-reward tradeoff." You get speed and low cost, but you no longer have the same level of protection as holding assets directly on the mainnet. Your assets are secured by the sidechain’s validators, not the entire Ethereum network.
Security Risks: The Bridge Problem
If sidechains are so useful, why do experts worry? Because the bridge is the weakest link. According to Chainalysis data, cross-chain bridges accounted for 65% of all DeFi hacks between 2020 and 2023, resulting in billions of dollars in losses.
The primary vulnerabilities include:
- Smart Contract Bugs: The code locking your funds might have a flaw. Even audited contracts can have edge-case errors.
- Validator Compromise: If hackers gain access to the private keys of the validator nodes, they can approve fraudulent withdrawals.
- Censorship: On federated bridges, validators can choose to ignore your withdrawal request, leaving your funds stuck indefinitely.
To mitigate these risks, many users adopt a "sleeping with one eye open" strategy. They only move the minimum amount of assets needed for immediate use onto the sidechain. The rest remains in a hardware wallet on the mainchain. This minimizes exposure if a bridge fails.

Real-World Examples: Polygon and Beyond
Let’s look at how this plays out in practice. Polygon is the most prominent sidechain connected to Ethereum. Its bridge allows users to move ETH in roughly 2-5 minutes. The cost is negligible compared to Ethereum’s average gas fees, which can spike to over $10 during busy periods.
Another example is Immutable X, a sidechain built specifically for NFTs. It processes thousands of trades per second with zero gas fees for users. However, Immutable X uses a ZK-Rollup technology, which is technically distinct from a traditional sidechain but serves a similar purpose: offloading activity from the mainchain while maintaining security through cryptographic proofs.
For enterprise applications, companies like Kaleido report that integrating a production-ready sidechain bridge takes 6-8 weeks. The complexity arises from configuring validator sets and implementing fraud-proof mechanisms. This highlights that while sidechains solve user-side friction, they introduce significant technical overhead for developers.
The Future: Modular Blockchains and Shared Security
The current model of sidechains is evolving. The industry is moving toward "modular blockchains," where execution, settlement, and data availability layers are separated. Projects like Ethereum’s Proto-Danksharding (EIP-4844) aim to reduce the cost of data storage on the mainchain, making it cheaper for sidechains and rollups to post their data there.
Additionally, new protocols like Chainlink CCIP (Cross-Chain Interoperability Protocol) are introducing decentralized oracle networks to manage cross-chain messages. This reduces reliance on centralized bridge operators and aims to create a more uniform standard for connectivity.
By 2027, analysts predict that sidechains and similar Layer 2 solutions will handle the majority of non-financial transactions. The goal is to achieve "shared security," where sidechains inherit the security guarantees of the mainchain without sacrificing performance. Until then, understanding the two-way peg remains essential for anyone navigating the crypto ecosystem.
Is it safe to keep my crypto on a sidechain?
It depends on the amount. Sidechains are generally safe for active trading and gaming due to low fees, but they carry higher risk than the mainchain. For long-term storage of large values, keep assets on the mainchain or in a hardware wallet. Only move what you need for immediate use to the sidechain.
What happens if a sidechain bridge gets hacked?
If a bridge is compromised, users may lose their funds permanently, especially if the hack involves validator key theft. In some cases, the bridge can be paused, preventing further withdrawals. Always check the security audit status of the bridge before using it.
How long does it take to bridge assets?
Deposits usually take 2-10 minutes, depending on the sidechain. Withdrawals are slower, often taking 1-2 days, because they require cryptographic verification from the mainchain to ensure security against double-spending.
Are sidechains part of the Bitcoin network?
Yes, Bitcoin has sidechains like Liquid and Rootstock. However, the concept is most widely used in the Ethereum ecosystem due to its smart contract capabilities. Bitcoin sidechains primarily focus on faster settlements and privacy rather than complex dApp functionality.
What is the difference between a sidechain and a Layer 2?
Sidechains operate independently with their own security model and validators. Layer 2 solutions (like Optimistic or ZK Rollups) rely on the mainchain for finality and security, posting data to the mainnet. Layer 2s are generally considered more secure but may have different cost structures.